Malware analysis Suspicious activity
4.9
$ 23.50
In stock
(418)
Product Description
Suspicious Activity Details in Nebula – Malwarebytes Business Support

Malware Analysis Framework v1.0

Diagram of the malware analysis methodology.

Intro to Malware Analysis: What It Is & How It Works - InfoSec

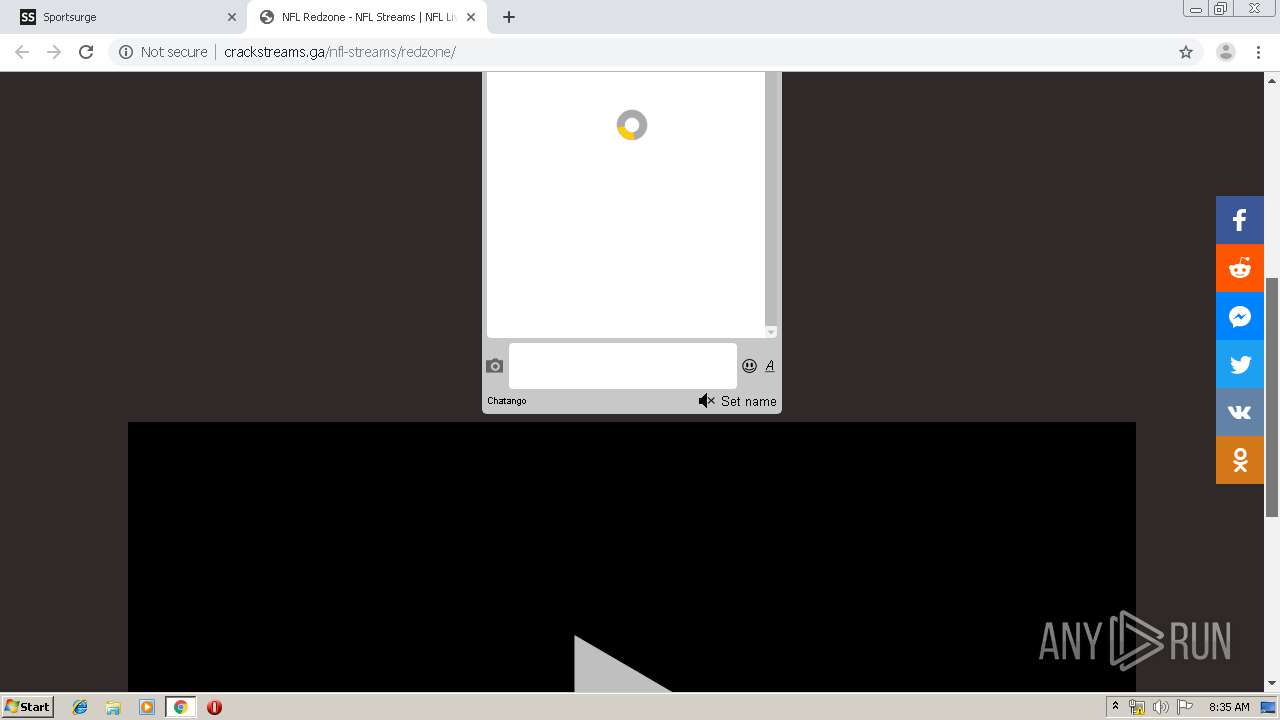
Malware Analysis Use Cases with ANY.RUN Sandbox - Security

REMnux toolkit for malware analysis version 7 released - Help Net

What is Malware Analysis

Remove McAfee Suspicious Activity Pop-ups [Virus Removal]
Highlight, take notes, and search in the book

Mastering Malware Analysis: A malware analyst's practical guide to combating malicious software, APT, cybercrime, and IoT attacks, 2nd Edition

Security Orchestration Use Case: Automating Malware Analysis









